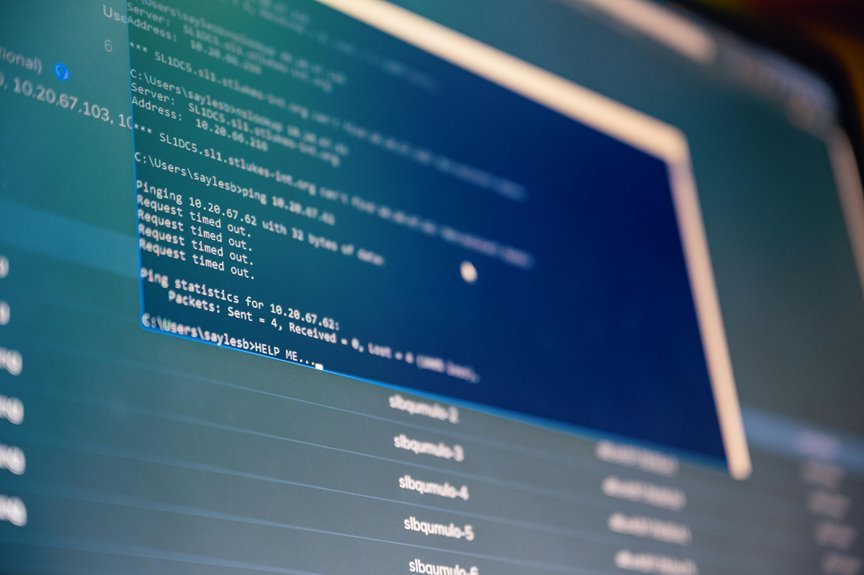
The address “10.70.122.5589” presents a significant anomaly within the realm of IPv4 addressing. With valid formats strictly defined, this particular instance exceeds acceptable octet values. Such discrepancies can disrupt network operations, leading to inefficient routing and communication. Understanding the ramifications of improper formatting is essential for effective network management. Further examination reveals the broader implications for resource allocation and security within modern infrastructures.
Components of the System Address
The system address comprises several critical components that facilitate effective communication and data management within computing environments.
Central to this are the address structure and address classification, which categorize different types of addresses for routing and identification purposes.
Understanding these components enables users to optimize network configurations, enhancing their autonomy in managing data pathways and ensuring efficient resource utilization within decentralized systems.
Applications and Use Cases
Exploring the applications and use cases of system addresses reveals their pivotal role in various computing environments.
Application scenarios include data packet routing, where system addresses facilitate efficient communication.
Use case examples extend to cloud computing, enabling resource allocation and identification, and IoT devices, which rely on precise addressing for seamless integration.
Such functionalities underscore the necessity of robust system address implementation in modern technology landscapes.
Implications for Network Management
Effective network management relies heavily on the integrity and organization of system addresses. Properly structured addresses enhance network efficiency by enabling streamlined data routing and communication.
Additionally, robust security protocols must be implemented to safeguard these addresses against unauthorized access. By prioritizing both organization and security, network administrators can foster a resilient infrastructure, ultimately ensuring seamless connectivity and safeguarding sensitive information from potential threats.
Conclusion
In conclusion, the analysis of the system address “10.70.122.5589” underscores the critical need for adherence to proper IP formatting to ensure efficient network performance and security. With the increasing complexity of cloud environments and IoT integrations, how can organizations effectively mitigate risks associated with improperly formatted addresses? By prioritizing accurate address structures, companies can enhance resource allocation, streamline communication, and fortify defenses against potential threats, significantly improving overall network management.